Sustainable NFV Networks for Beyond 5G
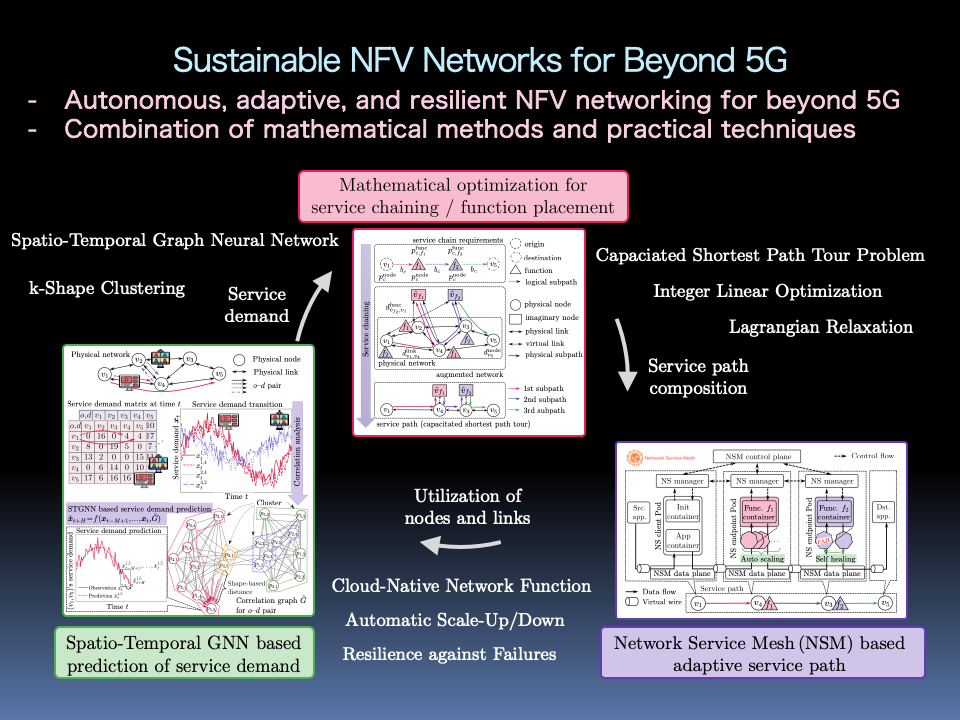
The next technology after 5G, i.e., Beyond 5G, has been expected to realize sustainable networks for creating new values in our society by adding new functionalities (i.e., ultra-low power consumption, ultra-security and reliability, autonomy, and scalability) to the 5G features (i.e., high speed and high capacity, low latency, and multiple simultaneous connections). Network functions virtualization (NFV) plays a key role to realize Beyond 5G. NFV is a new paradigm to achieve flexible and agile network services by decoupling network functions from proprietary hardware and running them on generic hardware as virtual network functions (VNFs). One of the challenging issues of NFV networking is optimal resource allocation where physical resources (e.g., physical servers and links) are appropriately allocated to a logical network (i.e., slice) or logical path (i.e., service path) according to users' demand. In addition, adaptability to spatio-temporal changes of users' demand and resiliency against failures of equipment/software are also important issues. In this research, we tackle these issues by combining mathematical methods (i.e., mathematical optimization and graph neural networks) and practical technologies (e.g., cloud-native network function (CNF)).
Selfish yet Optimal Control based on Game Theory
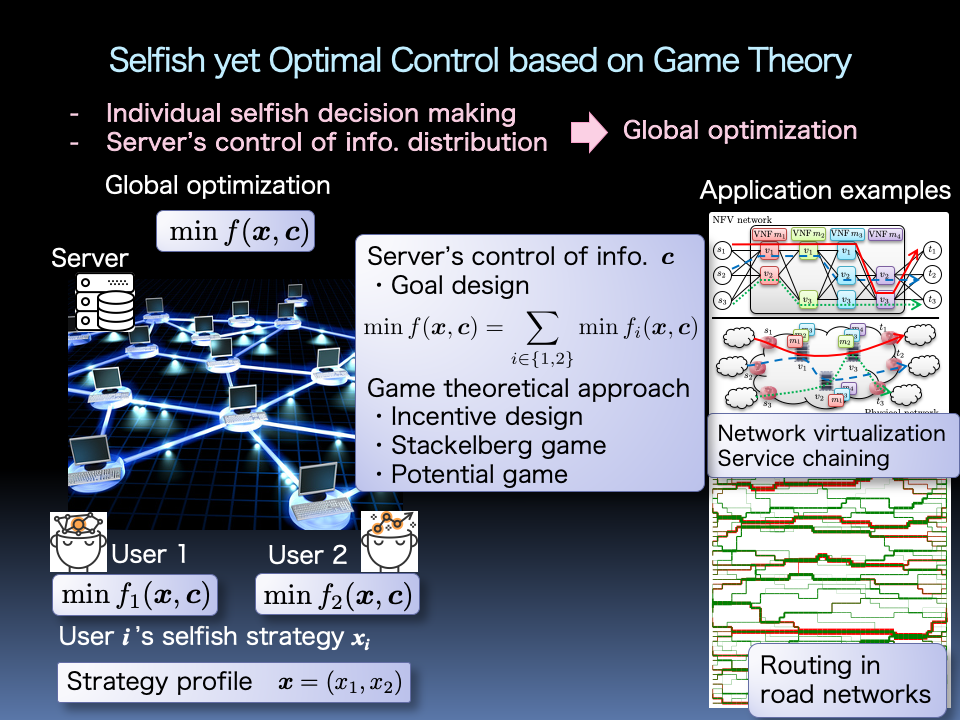
We have been supported by various social systems, e.g., the Internet and transportation networks. It is natural for individuals to desire better quality of experience (QoE), e.g., watching high quality video without delay and jitter, and faster travel to the destination. On the other hand, the resources of systems are limited. For example, in case of content distribution services, such resources can be the computation capacity of servers and network capacity. From the viewpoint of the overall systems, global optimization, e.g., improving the total QoE among all users, under the resource constraint is important. In this research, we aim to achieve the selfish yet optimal control, which can achieve the global optimization even under users' selfish decision making by appropriately controlling the perceived information at individuals.
Network Optimization for Large-Scale Content Distribution
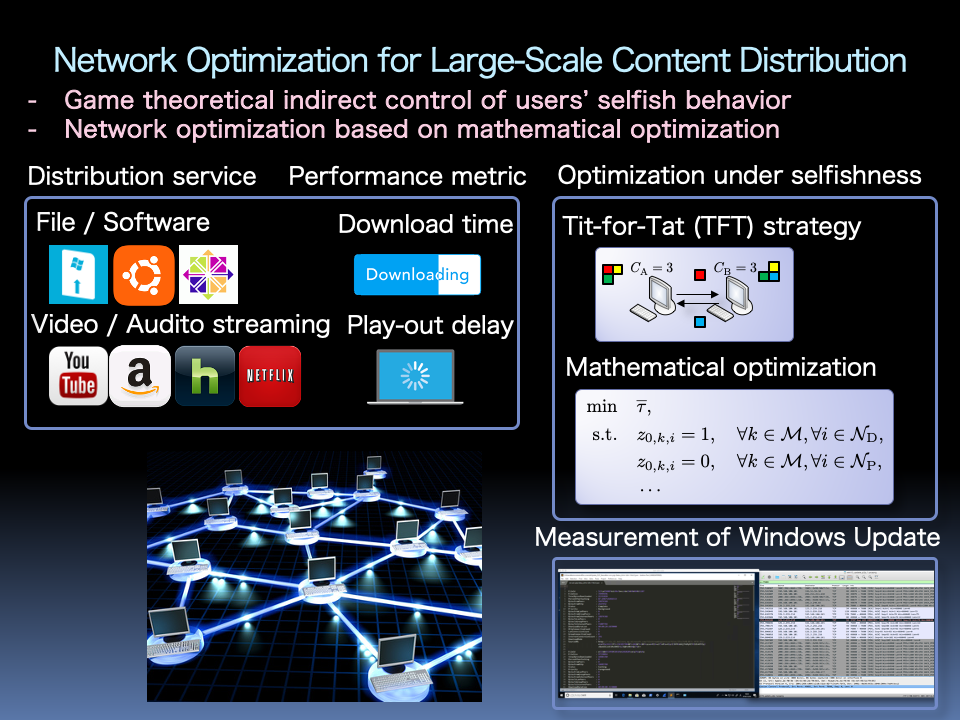
Software update and video streaming require massive and/or long-term content distribution. Specifically, new release of content causes steep increase of requests, making the distribution server a bottleneck. To tackle this problem, several systems, e.g., Windows update, recently apply peer-to-peer (P2P) file distribution where clients called peers upload retrieved fragments of the whole content, i.e., pieces, to other peers. However, some peers will not be willing to upload pieces to others, which are called free riders, due to communication overhead. tit-for-tat (TFT) strategy in game theory can suppress such free riding behavior by encouraging equivalent exchange of pieces among each pair of peers. In this research, we analyze the optimal design of the TFT-based P2P file distribution through mathematical optimization (e.g., linear optimization (programming) and integer linear optimization) and analytical models (e.g., flood model).
Human-Harmonized and Risk-Aware Automatic Evacuation Assistance
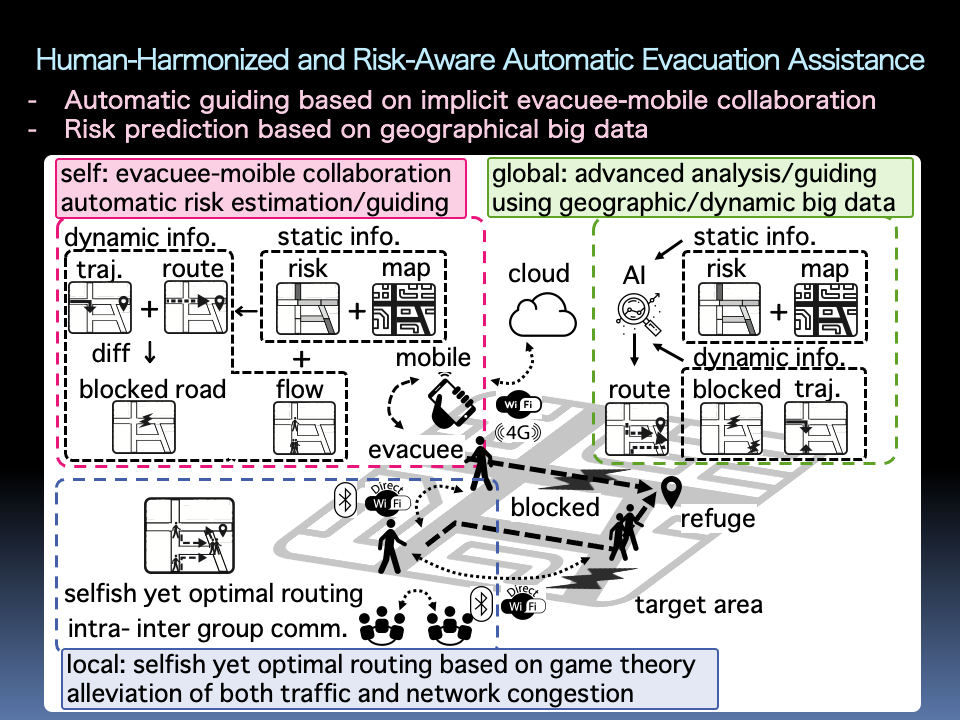
In the 2011 Great East Japan Earthquake, both fixed and mobile communication networks had been unavailable for long time and in wide areas, due to damage of communication infrastructures. As a result, it has been reported that there were many cases where evacuees and rescuers could not collect and distribute important information, e.g., damage information, evacuation information, and government information. In this research, we aim to achieve an evacuation assisting system that can speedily and safely navigate evacuees to appropriate refuges. Specifically, we tackle this problem by combining several functions (e.g., automatic road-state estimation and evacuation guiding under implicit collaboration among evacuees and their mobile devices, road network state information sharing among evacuees, and road network risk analysis using geographical big-data.)
Network Security in Blockchain Systems
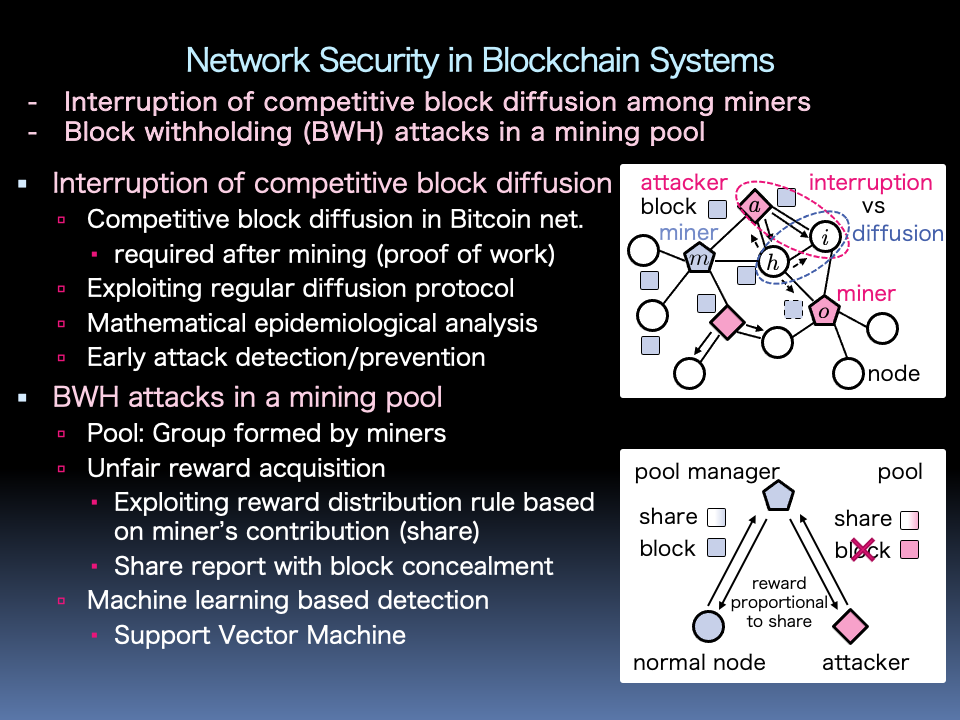
In the Bitcoin system, each miner (i.e., a special node that creates new blocks and broadcasts these blocks to the other miners) has to win both competitive block mining, i.e,. Proof of Work (PoW), and block diffusion over the Bitcoin network so as to acquire the system rewards. In this research, we focus on block diffusion delay attacks, where multiple attackers collude with a specific miner to disturb the propagation of blocks generated by competing miners. With the help of mathematical epidemiology, we develop a scalar (resp. network) standby-interrupted-retrieved-attackable (SIRA) models, which capture the information diffusion with interruption under a well-mixed population (resp. arbitrary networks). To acquire the rewards effectively, multiple miners tend to form a group called a pool to conduct PoW collaboratively. The pool manager will distribute rewards to members according to their contribution (called share). It has been pointed out that some malicious miners can realize block withholding (BWH) attacks that sabotage the mining process and gain more rewards by hiding found blocks and reporting their contribution. In this research, we aim to achieve early detection of BWH attacks with the help of machine learning approaches, e.g., support vector machine (SVM).
Distributed Cooperative Control for Large-Scale IoT Networks
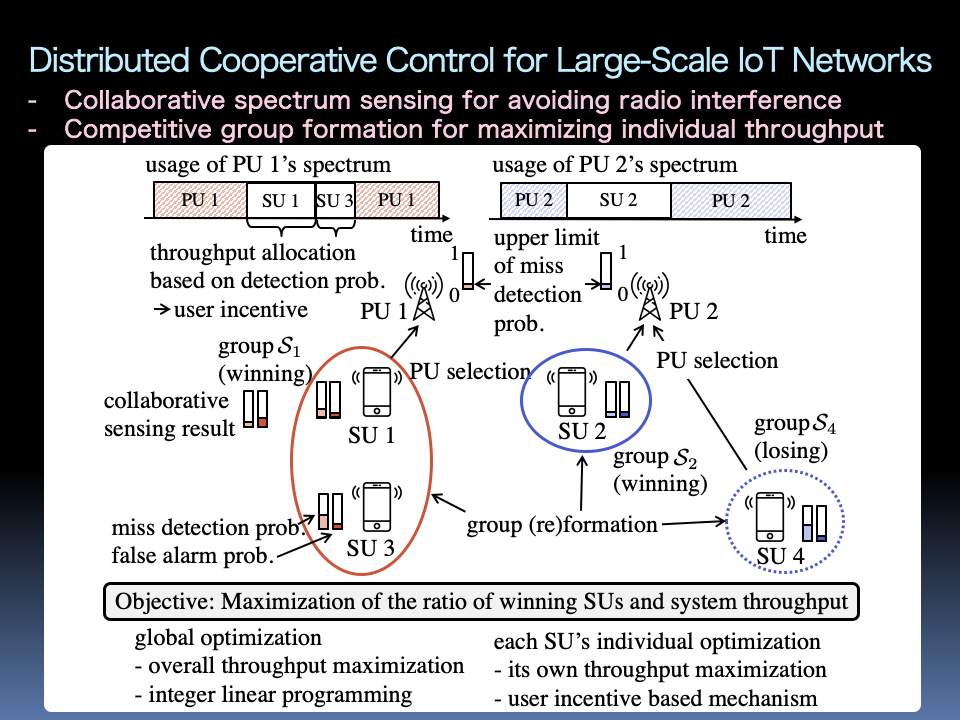
We have been faced with the new era of IoT, where various devices are connected to the Internet in addition to the conventional PCs and mobile phones. Most of the IoT devices are managed and controlled through wireless communications. On the other hand, most radio frequency bands have already been allocated to various existing systems. Thus, it is important to solve the spectrum exhaustion problem and to improve the spectrum utilization. To tackle this problem, cognitive radio has been studied, in which unlicensed users, i.e., secondary users (SUs), utilize the spectrum of a licensed user, i.e., primary user (PU), while avoiding interference in PU's communications. In this research, we aim to achieve a distributed cooperative control mechanism that can consider both cooperation among SUs for improving detection performance of PU's communication and competitive relationship among SUs to acquire individual communication opportunities.